This research introduces a novel defense mechanism against hardware security threats, specifically targeting SAT attacks on Integrated Circuits (ICs). By leveraging neural networks, the proposed method translates SAT-prone clauses into SAT-hard clauses, significantly enhancing the security of logic obfuscation techniques with minimal performance overhead.
Research Problem
The increasing reliance on offshore foundries for IC fabrication has heightened the risk of hardware security threats, including reverse engineering and intellectual property theft. Traditional logic obfuscation techniques are vulnerable to SAT attacks, which can decrypt the obfuscated circuits in a short time. This research aims to develop a robust defense mechanism that mitigates SAT attacks while maintaining low power, performance, and area (PPA) overheads.
Methods or Approach
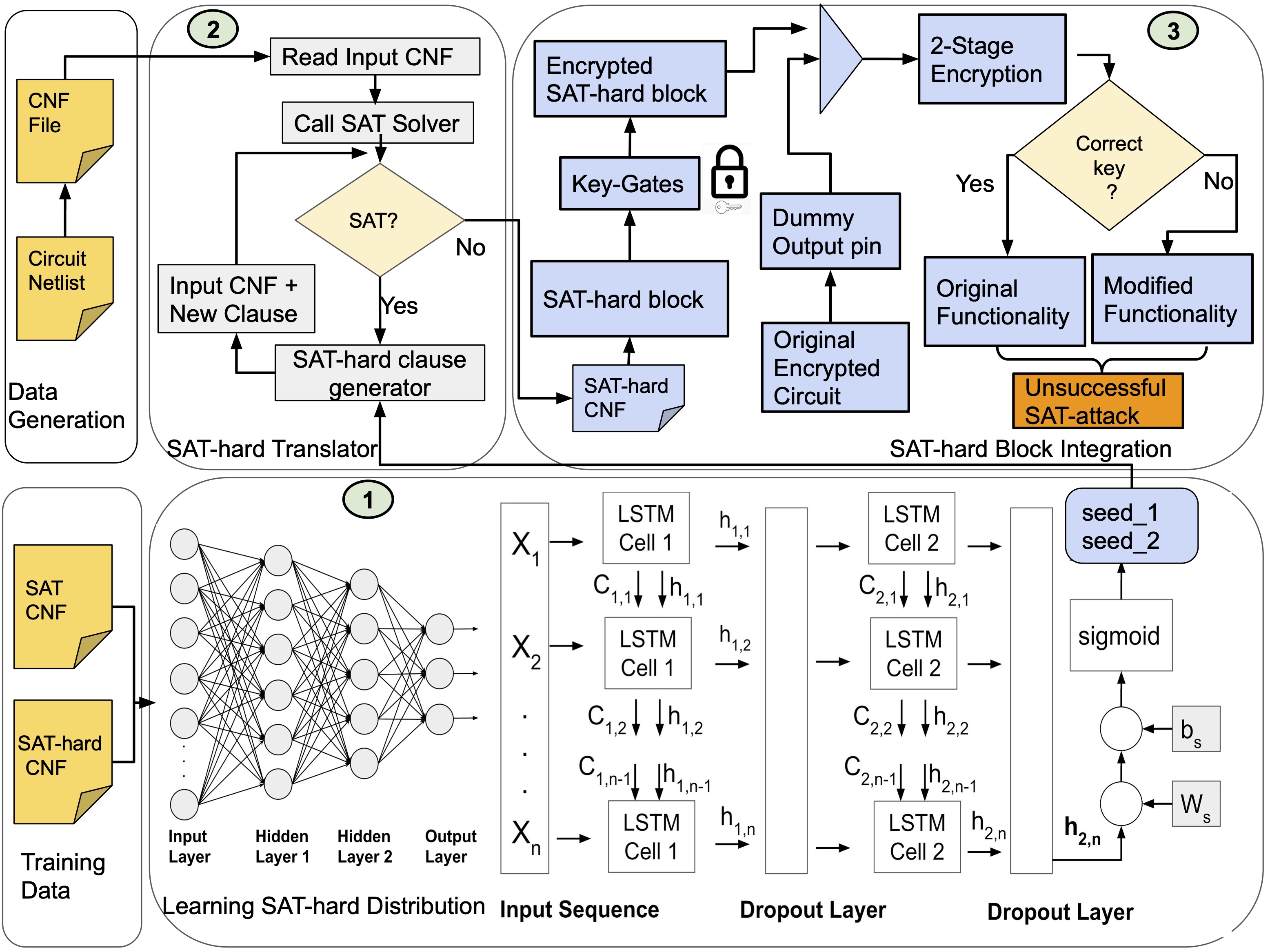
- Neural Network-Based SAT-Hard Clause Generator
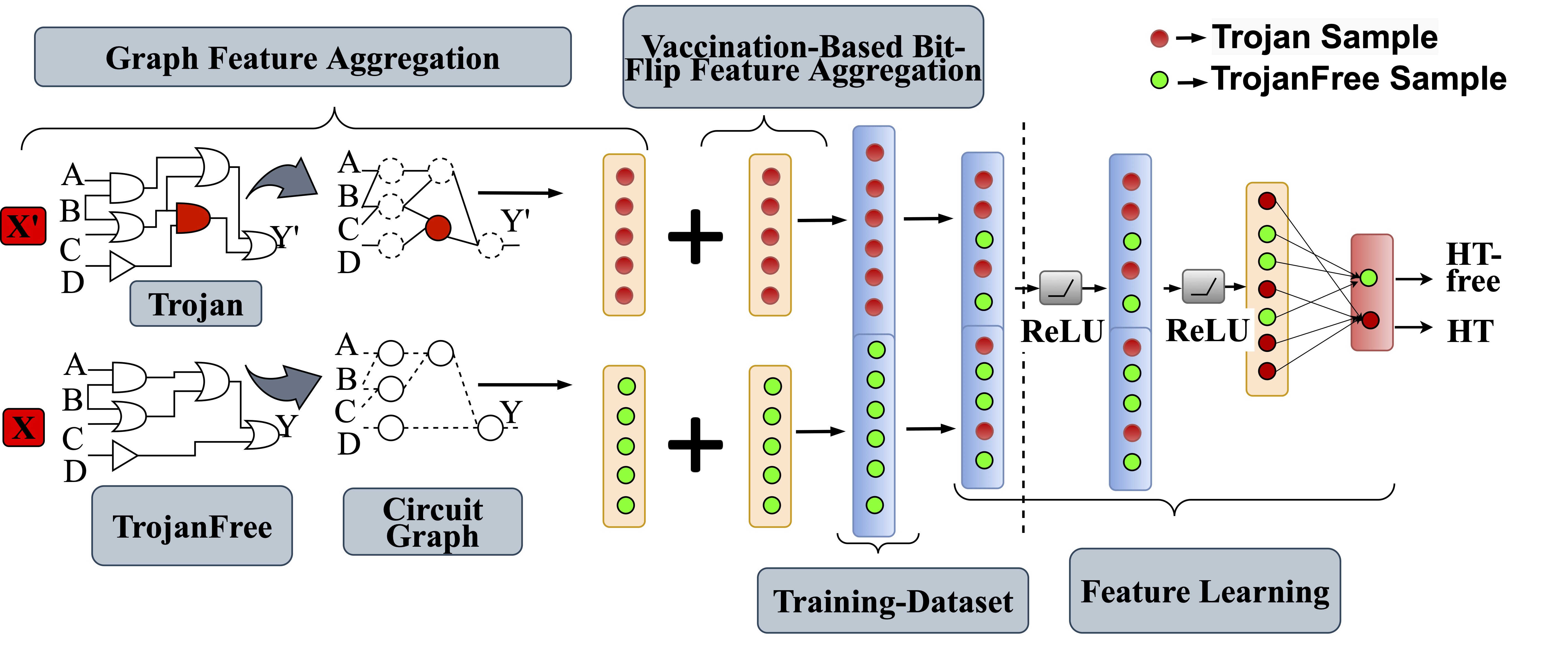
- Message Passing Neural Network (MPNN)
- LSTM Network
- Integration with Existing Circuits
Key Findings
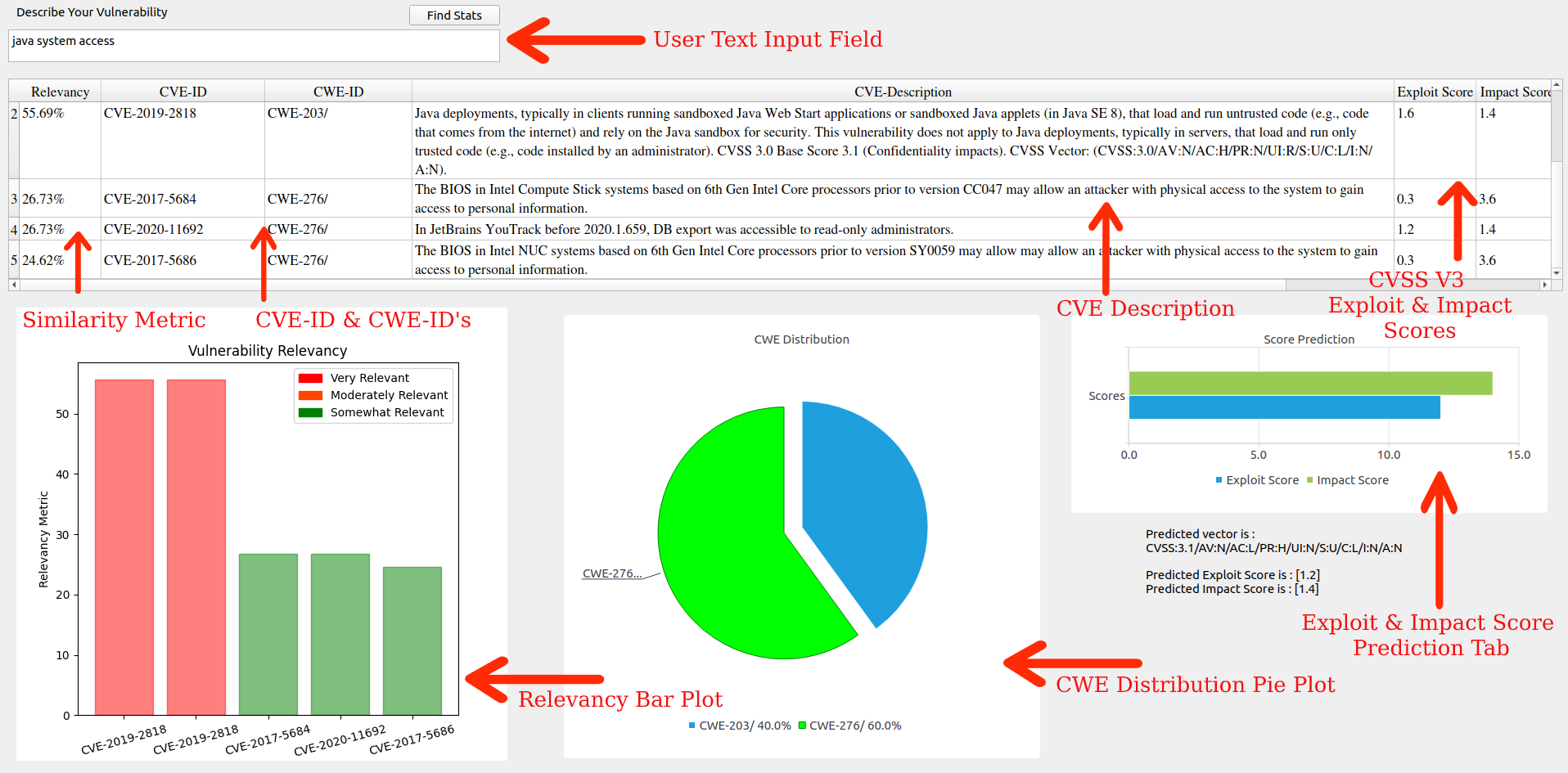
- Successfully defends against multiple state-of-the-art SAT attacks.
- Empirical evaluations on ISCAS'85 benchmarks demonstrate effectiveness.
- Minimal PPA overheads while preserving original functionality.
Impact and Future Applications
- Enhanced Security: Provides a robust defense mechanism against SAT attacks, protecting ICs from reverse engineering and IP theft.
- Low Overheads: Achieves high security with minimal impact on power, performance, and area.
- Scalability: Can be applied to various hardware security scenarios, making it a versatile solution for the semiconductor industry.
- Future Applications: Advanced hardware security and integration with emerging technologies.